+325 points
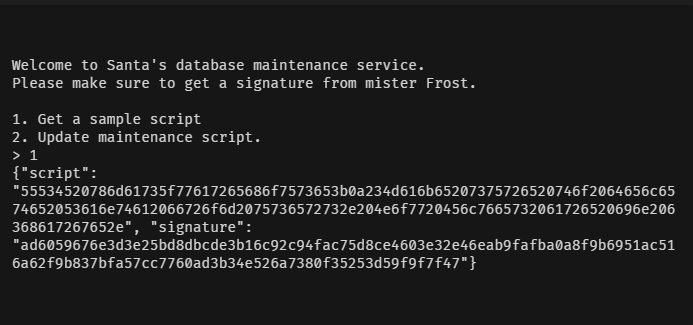
Warehouse Maintenance
Forge your own SHA512 signature using a length extension attack to execute signed SQL queries and get the flag.
+325 points
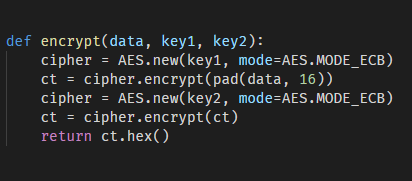
Meet me halfway
Double AES ECB encryption. Use a cryptographic trick to brute force 2 keys separately and decrypt the flag.
+325 points
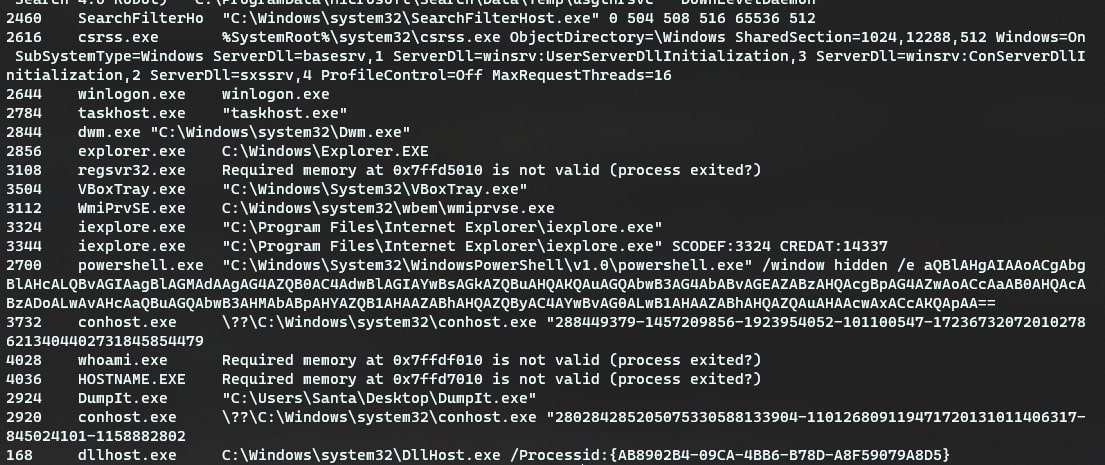
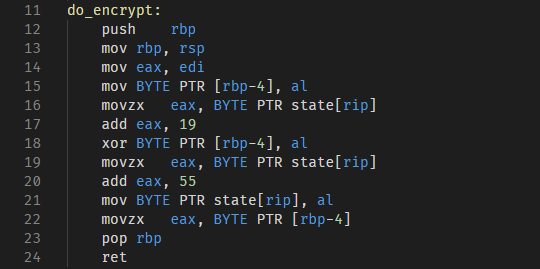
Intercept
A packet capture file with encrypted data, and reverse the assembly instructions to decrypt the data